Azure DDoS Protection Standard
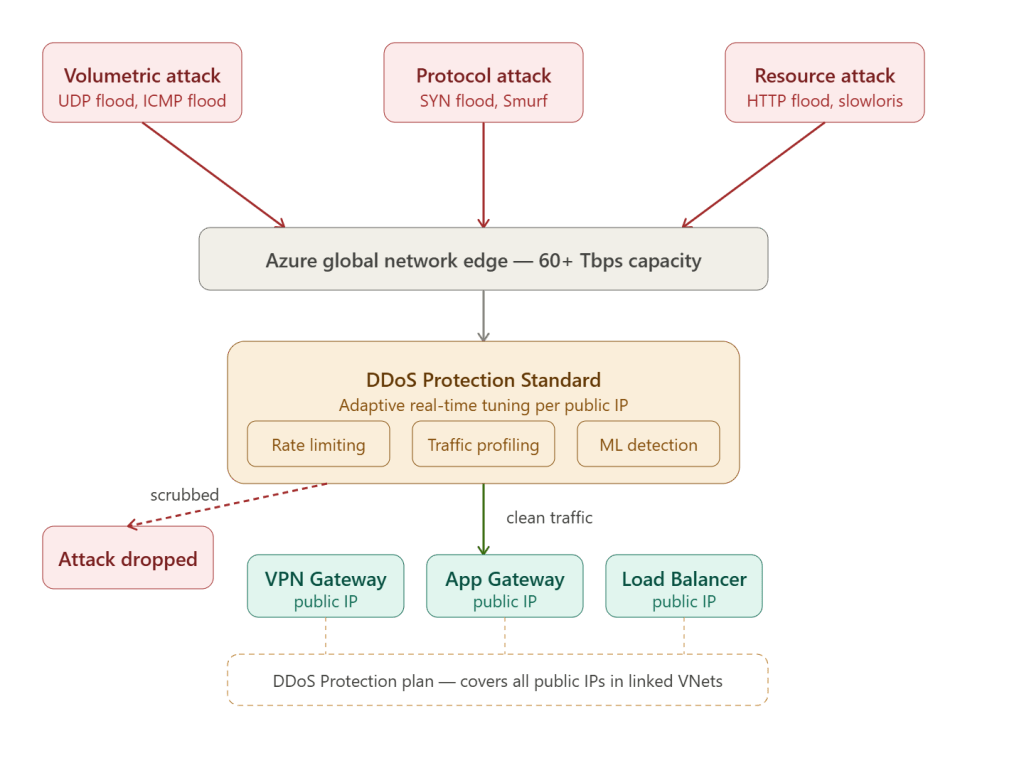
Azure DDoS Protection Standard is a managed, always-on service that detects and mitigates volumetric, protocol, and application-layer DDoS attacks against your Azure public IP addresses — automatically, without any configuration changes during an attack.
The Three Attack Categories It Defends Against
Layer 3/4 — Volumetric attacks
These flood your network bandwidth with massive traffic volumes — UDP floods, ICMP floods, amplification attacks (DNS, NTP, memcached). Azure absorbs these at the network edge using its global 60+ Tbps scrubbing capacity, before the traffic ever reaches your VNet or gateway.
Layer 3/4 — Protocol attacks
These exhaust connection state tables on firewalls, load balancers, and gateways. SYN floods send millions of half-open TCP connections; Smurf attacks abuse ICMP broadcasts. DDoS Protection mitigates these by validating TCP handshakes and rate-limiting malformed packets at the edge.
Layer 7 — Resource layer attacks
HTTP floods, Slowloris, and application-specific attacks target your app’s compute rather than your bandwidth. DDoS Protection Standard alone does not fully mitigate Layer 7 attacks — these require Azure WAF on Application Gateway or Azure Front Door working alongside DDoS Protection. The two services are designed to be used together for full-stack protection.
How Adaptive Tuning Works
This is the core differentiator versus the free Basic tier. DDoS Protection Standard builds a per-public-IP traffic baseline using machine learning:
Normal Monday traffic profile for your VPN Gateway public IP: - Avg 2,000 packets/sec - Peak 8,000 packets/sec - Protocol mix: 70% TCP, 20% UDP, 10% ICMP - Geographic distribution: CA, US, EUAttack detected when: - Packets jump to 4,000,000/sec ← 500× normal - 99% from single ASN in one region - All UDP port 53 (DNS amplification)Response: automatic mitigation within seconds - Rate limit traffic matching attack signature - Pass legitimate traffic through - Alert via Azure Monitor
Baselines are built per public IP, per protocol, per port — so the service understands what normal looks like for your VPN Gateway vs your Application Gateway vs your load balancer, and tuning is automatic as your traffic patterns change.
DDoS Protection Tiers Compared
| Feature | Basic (free) | Network (Standard) | IP Protection |
|---|---|---|---|
| Always-on monitoring | ✅ | ✅ | ✅ |
| Automatic attack mitigation | ✅ basic | ✅ advanced | ✅ advanced |
| Adaptive ML tuning per IP | ❌ | ✅ | ✅ |
| Attack analytics & metrics | ❌ | ✅ | ✅ |
| Attack mitigation reports | ❌ | ✅ | ✅ |
| Attack mitigation flow logs | ❌ | ✅ | ✅ |
| Azure Monitor alerts | ❌ | ✅ | ✅ |
| WAF policy integration | ❌ | ✅ | ✅ |
| DDoS Rapid Response (Microsoft experts) | ❌ | ✅ | ❌ |
| Cost protection (service credit) | ❌ | ✅ | ✅ |
| Scope | All Azure (shared) | Per VNet (plan) | Per public IP |
| Pricing | Free | ~$2,944/month + per IP | ~$199/IP/month |
Network Protection (the classic “Standard” tier) is applied at the VNet level via a DDoS Protection Plan — every public IP in all linked VNets is automatically covered.
IP Protection is a newer, per-IP option introduced for smaller deployments where you only need to protect a handful of public IPs without paying for a full plan.
What a DDoS Protection Plan Covers
A single DDoS Protection Plan can be linked to multiple VNets across multiple subscriptions in the same tenant. This is the right model for hub and spoke — one plan at the hub subscription level covers everything:
DDoS Protection Plan (resource group: rg-network-hub) ↓ linked toHub VNet → VPN Gateway public IP protected → Azure Firewall public IP protected → Bastion public IP protectedSpoke 4 (DMZ) → App Gateway public IP protected → Load Balancer public IP protected
The first 100 public IPs are included in the plan price. Beyond 100, you pay per additional IP.
Monitoring and Alerting
During and after an attack, DDoS Protection surfaces detailed metrics in Azure Monitor:
| Metric | What it shows |
|---|---|
Under DDoS attack | Boolean — 1 if attack active on this IP |
Inbound packets dropped DDoS | Packets/sec being scrubbed |
Inbound packets forwarded DDoS | Clean packets/sec passing through |
Inbound bytes DDoS | Raw attack volume in bytes/sec |
Mitigation reason | SYN flood, UDP flood, etc. |
Set an alert rule on Under DDoS attack = 1 to fire a notification to your security team or trigger a Logic App / n8n workflow the moment an attack begins.
When Should You Enable It?
Enable DDoS Protection Standard when any of these are true
Any public-facing production workload with real business impact if taken offline — an internet-facing Application Gateway, a VPN Gateway handling thousands of remote users, or a load balancer fronting a revenue-generating application — warrants the protection. The ~$3K/month cost is trivial compared to the revenue loss and incident response cost of a successful multi-hour DDoS attack.
You also need it when compliance frameworks require it. PCI-DSS, HIPAA, and ISO 27001 environments often require documented DDoS mitigation controls, and DDoS Protection Standard gives you the attack reports and flow logs needed to satisfy auditors.
The cost protection feature is a practical reason too — if an attack causes your Azure compute or bandwidth costs to spike (autoscaled VMs spun up to handle flood traffic, for example), Microsoft will credit those costs back when DDoS Protection was enabled.
You can skip it when
Dev/test environments, internal-only workloads with no public IPs, and resources entirely behind Azure Front Door or a third-party CDN that absorbs attacks upstream don’t need the plan — the Basic tier’s shared protection is sufficient, and the CDN/Front Door layer already absorbs volumetric attacks before they reach your origin.
In a Hub and Spoke Context
The recommended placement is one DDoS Protection Plan at the hub subscription, linked to the hub VNet and any spoke VNets that have public IPs (typically the DMZ spoke with App Gateway and WAF). Pair it with Azure Firewall for Layer 3/4 east-west filtering and Azure WAF on Application Gateway for Layer 7 protection, and you have defence-in-depth across all three attack categories.