What is Azure VPN Gateway?
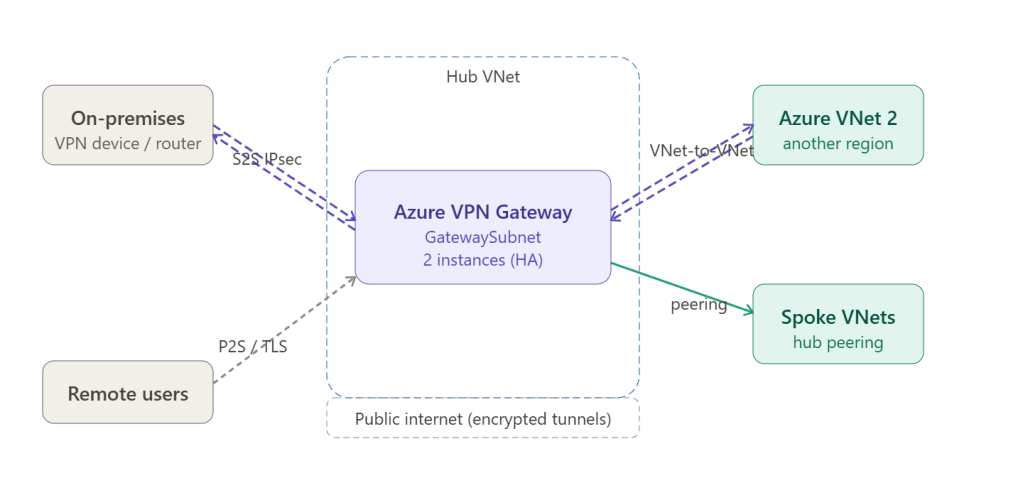
An Azure VPN Gateway is a managed network gateway service that sends encrypted traffic between an Azure Virtual Network and an on-premises location (or another Azure VNet) over the public internet using IPsec/IKE tunnels. It’s the primary service that bridges your on-premises network to Azure in a hub and spoke topology.
Three Connection Types
Site-to-Site (S2S) connects your entire on-premises network to Azure over an IPsec/IKE tunnel. Your on-premises VPN device (router or firewall) terminates the tunnel. This is the most common type used in hub and spoke.
Point-to-Site (P2S) connects individual remote devices (laptops, phones) directly to the Azure VNet. Uses OpenVPN, SSTP, or IKEv2 protocols. No on-premises device required — just a VPN client app.
VNet-to-VNet connects two Azure VNets in different regions using the same IPsec tunnel mechanism as S2S. For same-region connections, VNet peering is cheaper and faster — VNet-to-VNet is mainly used cross-region or across subscriptions/tenants.
How It Works Internally
On-premises VPN device ↓ IPsec/IKE tunnel (encrypted)Azure VPN Gateway (2 VM instances in GatewaySubnet) ↓ internal routingHub VNet → UDR propagation → Spoke VNets
The gateway always deploys as two instances for high availability. You choose between active-passive (one standby, ~10s failover) or active-active (both instances forward traffic simultaneously, faster failover).
SKUs — Full Breakdown
SKUs are grouped into generations. Generation 2 is current and recommended for all new deployments.
Generation 1 (legacy — avoid for new deployments)
| SKU | Max throughput | S2S tunnels | P2S connections | BGP | Zone-redundant |
|---|---|---|---|---|---|
| Basic | 100 Mbps | 10 | 128 | ❌ | ❌ |
| VpnGw1 | 650 Mbps | 30 | 250 | ✅ | ❌ |
| VpnGw2 | 1 Gbps | 30 | 500 | ✅ | ❌ |
| VpnGw3 | 1.25 Gbps | 30 | 1,000 | ✅ | ❌ |
Generation 2 (current — recommended)
| SKU | Max throughput | S2S tunnels | P2S connections | BGP | Zone-redundant |
|---|---|---|---|---|---|
| VpnGw1 | 650 Mbps | 30 | 250 | ✅ | ❌ |
| VpnGw2 | 1 Gbps | 30 | 500 | ✅ | ❌ |
| VpnGw3 | 1.25 Gbps | 30 | 1,000 | ✅ | ❌ |
| VpnGw4 | 5 Gbps | 100 | 5,000 | ✅ | ❌ |
| VpnGw5 | 10 Gbps | 100 | 10,000 | ✅ | ❌ |
| VpnGw1AZ | 650 Mbps | 30 | 250 | ✅ | ✅ |
| VpnGw2AZ | 1 Gbps | 30 | 500 | ✅ | ✅ |
| VpnGw3AZ | 1.25 Gbps | 30 | 1,000 | ✅ | ✅ |
| VpnGw4AZ | 5 Gbps | 100 | 5,000 | ✅ | ✅ |
| VpnGw5AZ | 10 Gbps | 100 | 10,000 | ✅ | ✅ |
The AZ suffix means the gateway is deployed across Availability Zones — its instances span physically separate datacentre buildings, protecting against a full zone failure. This is the right choice for production workloads with strict uptime requirements.
SKU Selection Guide
| Scenario | Recommended SKU |
|---|---|
| Dev/test only, no BGP needed | Basic |
| Small org, <30 branch offices | VpnGw1AZ |
| Mid-size enterprise | VpnGw2AZ or VpnGw3AZ |
| Large enterprise, many tunnels | VpnGw4AZ |
| Very high throughput (10 Gbps) | VpnGw5AZ |
| High SLA required in production | Any AZ SKU |
Key Concepts to Know
BGP (Border Gateway Protocol) — enables dynamic route exchange between Azure and your on-premises router. Without BGP, you must manually define every on-premises subnet in the Local Network Gateway. With BGP, routes are exchanged automatically. Required for active-active configurations and most enterprise setups.
GatewaySubnet — a dedicated subnet in your hub VNet that must be named exactly GatewaySubnet. Minimum /27 (32 addresses), recommended /26 or larger for future gateway coexistence (VPN + ExpressRoute). No other resources should be placed in this subnet.
Local Network Gateway — an Azure resource that represents your on-premises VPN device. You define its public IP address and the address space of your on-premises network here.
Active-Active mode — both gateway instances are active simultaneously, each with its own public IP. Your on-premises VPN device must support two tunnels. Provides near-zero downtime failover and higher aggregate throughput.
IKE versions — the gateway supports IKEv1 and IKEv2. IKEv2 is preferred — it’s faster to negotiate, more secure, and required for P2S with IKEv2 clients.
VPN Gateway vs ExpressRoute Gateway
| VPN Gateway | ExpressRoute Gateway | |
|---|---|---|
| Transport | Public internet (encrypted) | Private MPLS circuit (unencrypted at layer) |
| Max throughput | 10 Gbps (VpnGw5AZ) | Up to 100 Gbps (UltraPerformance) |
| Latency | Variable (internet) | Consistent, low latency |
| Cost | Lower | Higher (circuit + gateway) |
| Use case | Most enterprises | Financial, healthcare, high-compliance |
In many enterprise deployments both coexist in the same GatewaySubnet — ExpressRoute as the primary path, VPN as the failover.