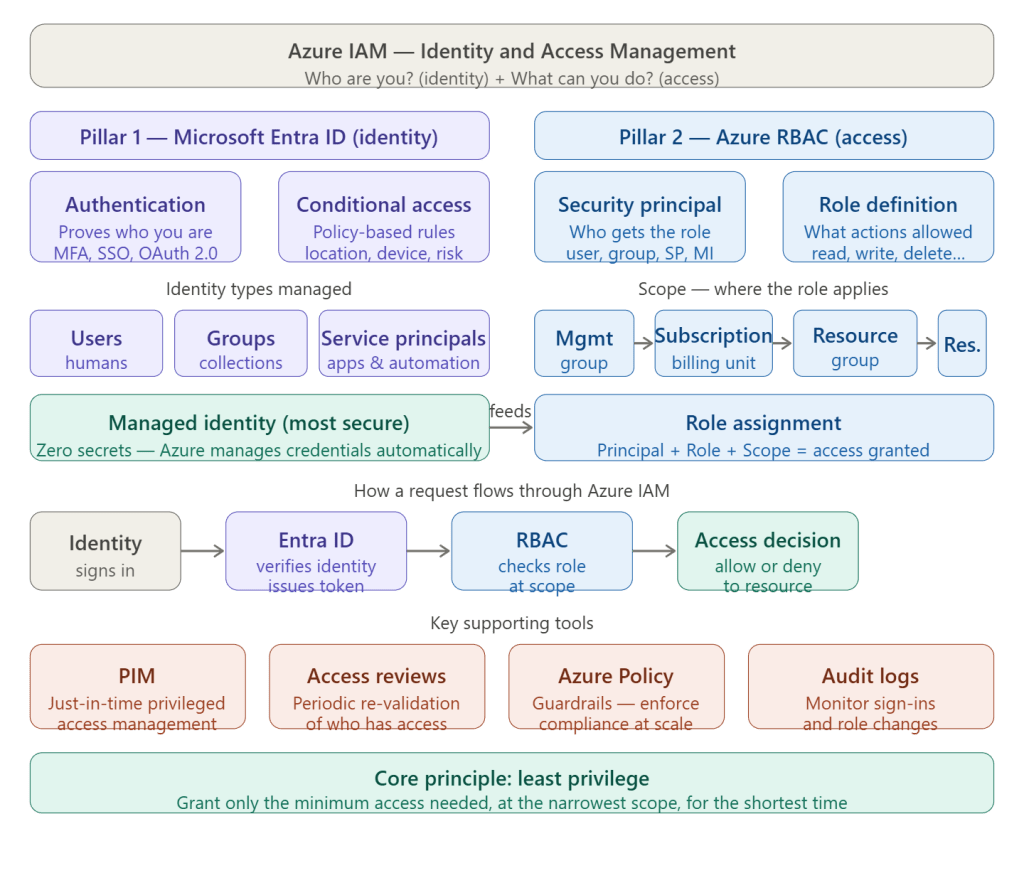
Azure IAM is best understood as two interlocking systems working together. Let me show you the big picture first, then how a request actually flows through it.Azure IAM is built around one question answered in two steps: who are you? and what are you allowed to do? Those two steps map to two distinct systems that work together.
Pillar 1 — Microsoft Entra ID (formerly Azure Active Directory): identity
This is the authentication layer. It answers “who are you?” by verifying credentials and issuing a token. It manages every type of identity in Azure: human users, guest accounts, groups, service principals (for apps and automation), and managed identities (the zero-secret identity type where Azure owns the credential). It also enforces Conditional Access policies — rules that say things like “only allow login from compliant devices” or “require MFA when signing in from outside the corporate network.”
Pillar 2 — Azure RBAC (Role-Based Access Control): access
This is the authorization layer. It answers “what can you do?” once identity is proven. RBAC works through three concepts combined into a role assignment:
- A security principal — the identity receiving the role (user, group, service principal, or managed identity)
- A role definition — what actions are permitted (e.g.,
Owner,Contributor,Reader, or a custom role) - A scope — where the role applies, which follows a hierarchy: Management Group → Subscription → Resource Group → individual Resource
A role assigned at a higher scope automatically inherits down. Give someone Reader on a subscription and they can read everything inside it.
The supporting tools
Three tools round out a mature IAM setup. PIM (Privileged Identity Management) implements just-in-time access — instead of being a permanent Owner, you request elevation for 2 hours, do the work, and the permission expires automatically. Access Reviews let you periodically re-validate who still needs access, cleaning up stale assignments. Azure Policy enforces guardrails at scale — for example, preventing anyone from assigning Owner at the subscription level without an approval workflow.
The core principle threading through all of it
Least privilege: grant the minimum role, at the narrowest scope, for the shortest duration. This is what PIM, custom roles, and resource-group-level assignments all support — shrinking the blast radius if any identity is ever compromised.