An Azure Landing Zone is basically the foundation of your cloud environment—a pre-configured setup in Microsoft Azure that ensures everything you build is secure, scalable, and well-organized from day one.
🧱 What is an Azure Landing Zone?
Think of it like setting up the rules and structure before building a city.
An Azure Landing Zone provides:
- A standardized environment
- Built using best practices (security, governance, networking)
- Ready for workloads (apps, data, services) to be deployed
It’s part of the Cloud Adoption Framework (CAF) by Microsoft.
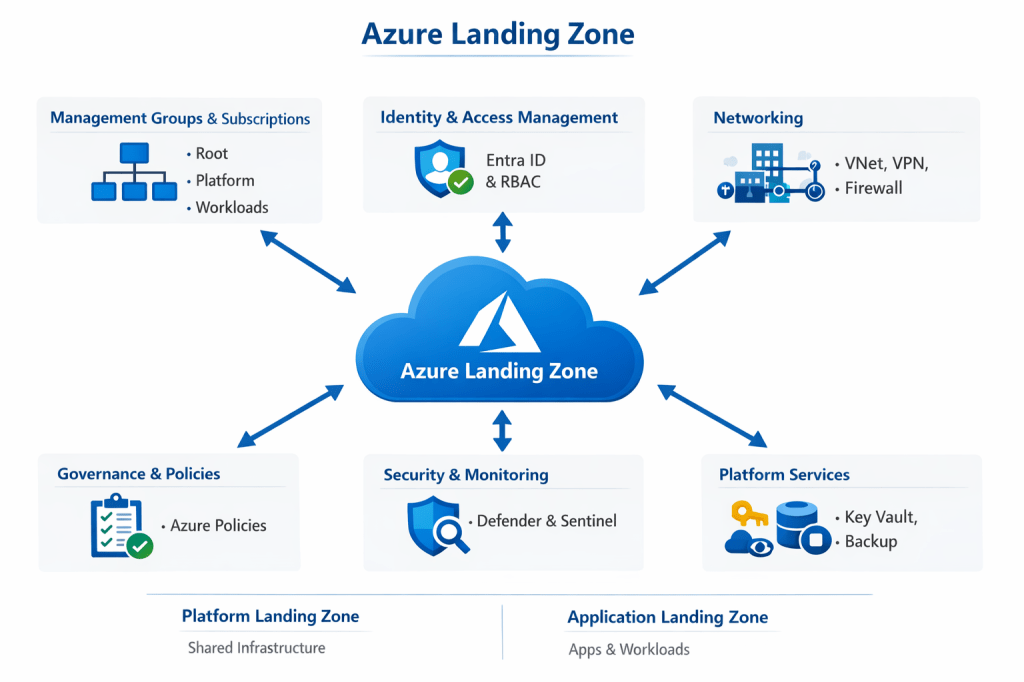
🧩 Core Components
1. Management Groups & Subscriptions
- Organizes resources hierarchically
- Example:
- Root → Platform → Landing Zones → Workloads
2. Identity & Access Management
- Uses Microsoft Entra ID
- Controls:
- Who can access what
- Role-Based Access Control (RBAC)
3. Networking
- Hub-and-spoke or Virtual WAN architecture
- Includes:
- VNets, subnets
- Private endpoints
- Firewalls
4. Governance & Policies
- Uses Azure Policies to enforce rules:
- Allowed regions
- Naming conventions
- Security requirements
5. Security & Monitoring
- Tools like:
- Microsoft Defender for Cloud
- Microsoft Sentinel
- Logging, alerts, compliance tracking
6. Platform Services
- Shared services like:
- Key Vault
- DNS
- Backup
- Example: Azure Key Vault
🏗️ Types of Landing Zones
1. Platform Landing Zone
- Shared infrastructure (networking, identity, security)
2. Application Landing Zone
- Where actual apps/workloads run
🧠 Why It Matters (Interview Gold)
- Prevents chaos and misconfiguration
- Enforces security & compliance at scale
- Enables automation (IaC + CI/CD)
- Supports multi-team environments
💬 2-Minute Interview Answer (Polished)
“An Azure Landing Zone is a pre-configured, enterprise-ready environment in Microsoft Azure that provides the foundational setup for deploying workloads securely and consistently. It includes key components like management groups and subscriptions for organization, identity and access management through Entra ID, hub-and-spoke networking, and governance using Azure Policies.
It also integrates security and monitoring tools like Defender for Cloud and Sentinel, along with shared platform services such as Key Vault. The goal is to enforce best practices from the start—covering security, compliance, and scalability—so teams can deploy applications without worrying about underlying infrastructure standards.
In practice, I’ve seen Landing Zones implemented using Infrastructure as Code with tools like Terraform or Bicep, combined with CI/CD pipelines, to ensure everything is repeatable and governed automatically.”