Kong API Gateway is a lightweight, fast, and flexible solution for managing APIs. It acts as a reverse proxy, sitting between clients (e.g., applications, users) and upstream services (e.g., APIs, microservices). Kong provides features like request routing, authentication, rate limiting, logging, and monitoring.
How Kong API Gateway Works
- Clients Make Requests:
- Applications or users send HTTP/HTTPS requests to the Kong Gateway.
- Kong Intercepts Requests:
- Kong routes these requests to the appropriate upstream service based on configuration rules.
- It can apply middleware plugins for authentication, rate limiting, transformations, logging, and more.
- Plugins Process Requests:
- Plugins enhance Kong’s functionality. For example:
- Authentication plugins: Validate tokens or credentials.
- Rate limiting plugins: Control the number of requests allowed.
- Logging plugins: Send logs to monitoring systems.
- Transformation plugins: Modify requests or responses.
- Plugins enhance Kong’s functionality. For example:
- Request Routed to Upstream:
- Kong forwards the processed request to the backend service (API or microservice).
- Upstream Service Responds:
- The upstream service sends the response back to Kong.
- Kong Returns Response:
- Kong optionally applies response transformations (e.g., add headers) before sending the response to the client.
Key Components of Kong
| Component | Description |
| Proxy | Routes incoming requests to the appropriate upstream service. |
| Admin API | Manages Kong configurations, including services, routes, and plugins. |
| Database | Stores Kong configuration data (e.g., PostgreSQL or Cassandra). |
| Plugins | Extend Kong’s functionality (e.g., authentication, monitoring, logging). |
| Upstream Services | The actual backend services or APIs that Kong forwards requests to. |
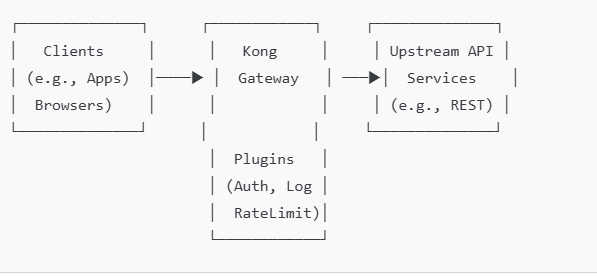
Diagram: How Kong API Gateway Works
Here’s a simplified visual representation of Kong’s architecture:
Detailed Kong Workflow with Features
- Request Received by Kong
A request like https://api.example.com/v1/orders reaches Kong.
Kong matches the request with:- A route: (e.g., /v1/orders).
- A service: The upstream API serving the request.
- Plugins Applied
Kong processes the request with active plugins for:- Authentication: Checks API keys, OAuth tokens, or LDAP credentials.
- Rate Limiting: Ensures the client doesn’t exceed allowed requests.
- Logging: Sends logs to external systems like ElasticSearch or Splunk.
- Routing to Upstream
After processing, Kong forwards the request to the appropriate upstream service.
Example:- Route /v1/orders → Upstream service http://orders.example.com.
- Response Handling
The upstream service responds to Kong.
Plugins can modify responses (e.g., masking sensitive data). - Response Sent to Client
Kong sends the final response back to the client.
Common Use Cases
- API Security:
- Add layers of authentication (e.g., JWT, OAuth, mTLS).
- Enforce access control policies.
- Traffic Control:
- Apply rate limiting or request throttling to prevent abuse.
- API Management:
- Route requests to appropriate backend APIs or microservices.
- Monitoring & Analytics:
- Capture detailed logs and metrics about API usage.
- Ease of Scalability:
- Kong can scale horizontally, ensuring high availability and performance.
Advanced Configurations
- Load Balancing: Kong can distribute requests across multiple instances of an upstream service.
- mTLS: Mutual TLS ensures secure communication between Kong and clients or upstream services.
- Custom Plugins: You can write custom Lua or Go plugins to extend Kong’s capabilities.