Managing cross-spoke traffic—often called East-West traffic—is a critical design challenge in large-scale Azure environments. As of 2026, the shift toward Zero Trust and automated routing has made traditional manual User-Defined Routes (UDRs) less sustainable for large enterprises.
Depending on your scale and security requirements, here are the preferred strategies for managing this traffic.
1. The Modern Enterprise Standard: Azure Virtual WAN (vWAN)
For environments with dozens or hundreds of spokes, Azure Virtual WAN with a Secured Hub is the gold standard. It replaces the manual effort of managing peering and route tables.
- How it works: You deploy a Virtual Hub and connect spokes to it. By enabling Routing Intent, you tell Azure to automatically attract all East-West traffic to an Azure Firewall (or supported third-party NVA) within the hub.
- Why it’s preferred:
- Auto-propagation: No need to manually create UDRs in every spoke to point to a central firewall; the hub manages the route injection.
- Transitive Routing: vWAN provides “any-to-any” connectivity by default, solving the non-transitive nature of standard VNet peering.
- Scale: It is designed to handle thousands of connections and massive throughput across multiple regions.
2. The Granular Control Approach: Hub-and-Spoke with Azure Virtual Network Manager (AVNM)
If you prefer a traditional Hub-and-Spoke model but want to avoid the “UDR Hell” of manual updates, Azure Virtual Network Manager (AVNM) is the strategic choice.
- Strategy: Use AVNM to define Network Groups (e.g., “Production-Spokes”). AVNM can then automatically:
- Create and manage VNet peerings.
- Deploy Admin Rules (security) and Routing Rules (UDRs) across all VNets in a group.
- Best For: Environments that require high customization or the use of specific third-party NVAs that may not yet be fully integrated into the vWAN “Managed” model.
3. The “Service-First” Strategy: Azure Private Link
Not all cross-spoke traffic needs to be “network-level” (Layer 3). For communication between applications (e.g., a web app in Spoke A talking to a database in Spoke B), Private Link is often superior to VNet peering.
- Strategy: Instead of peering the entire VNets, expose the specific service in Spoke B via a Private Link Service. Spoke A then consumes it via a Private Endpoint.
- Why it’s preferred:
- Isolation: It eliminates the risk of lateral movement across the network because the VNets are not actually “connected.”
- IP Overlap: It allows spokes with overlapping IP ranges to communicate, which is impossible with standard peering.
- Security: Traffic stays on the Microsoft backbone and is mapped to a specific resource, reducing the attack surface.
4. Architectural Comparison: At-a-Glance
| Feature | Standard Peering + UDR | Virtual WAN (Secured Hub) | Private Link |
| Complexity | High (Manual) | Low (Automated) | Medium (Per-service) |
| Transitivity | None (requires NVA/UDR) | Native | N/A (Service-based) |
| Scale | Hard to maintain | Excellent | Excellent |
| Security | NSG + Firewall NVA | Integrated Firewall | Least Privilege (Resource-level) |
5. Critical Best Practice: “Zero Trust” at the Spoke
Regardless of the routing strategy, large environments should implement Micro-segmentation within the spokes.
- NSGs and ASGs: Use Network Security Groups (NSGs) combined with Application Security Groups (ASGs) to control traffic between subnets within the same spoke.
- Explicit Outbound (2026 Change): Note that as of March 31, 2026, Azure has retired “Default Outbound Access.” You must now explicitly define outbound paths (NAT Gateway or Firewall) for all spokes, which prevents accidental “leaking” of traffic to the internet while managing your internal East-West flows.
Designing a large-scale Azure environment from scratch in 2026 requires moving away from “bespoke” networking toward a Productized Infrastructure model.
The most robust strategy follows the Azure Landing Zone (ALZ) conceptual architecture, utilizing Azure Virtual WAN (vWAN) as the connectivity backbone. This setup minimizes manual routing while providing maximum security.
1. The Foundation: Management Group Hierarchy
Before touching a VNet, you must organize your governance. Use Management Groups to enforce “Guardrails” (Azure Policy) that automatically configure networking for every new subscription.
- Root Management Group
- Platform MG: Contains the
Connectivity,Identity, andManagementsubscriptions. - Landing Zones MG: * Corp MG: For internal workloads (connected to the Hub).
- Online MG: For internet-facing workloads (isolated or DMZ).
- Sandbox MG: For disconnected R&D.
- Platform MG: Contains the
2. The Network Backbone: Virtual WAN with Routing Intent
In a greenfield 2026 design, Virtual WAN (Standard SKU) is the preferred “Hub.” It acts as a managed routing engine.
The “Routing Intent” Strategy
Traditional hubs require you to manually manage Route Tables (UDRs) in every spoke. With Routing Intent enabled in your Virtual Hub:
- Centralized Inspection: You define that “Private Traffic” (East-West) must go to the Azure Firewall in the Hub.
- Auto-Propagation: Azure automatically “attracts” the traffic from the spokes to the Firewall. You no longer need to write a
0.0.0.0/0or10.0.0.0/8UDR in every spoke. - Inter-Hub Routing: If you expand to another region (e.g., East US to West Europe), vWAN handles the inter-region routing natively without complex global peering strings.
3. The Security Strategy: Micro-segmentation
Don’t rely solely on the central Firewall; it’s too “coarse” for large environments. Use a layered approach:
- North-South (Internet): Managed by Azure Firewall Premium in the vWAN Hub (IDPS, TLS Inspection).
- East-West (Cross-Spoke): Managed by Routing Intent + Azure Firewall.
- Intra-Spoke (Subnet-to-Subnet): Use Network Security Groups (NSGs) and Application Security Groups (ASGs).
- Tip: Use Azure Virtual Network Manager (AVNM) to deploy “Security Admin Rules” that stay at the top of the NSG stack across all spokes, preventing developers from accidentally opening SSH/RDP to the world.
4. The “Subscription Vending” Machine
In 2026, you shouldn’t “build” a spoke; you should “vend” it. When a team needs a new environment:
- A CI/CD pipeline (Terraform/Bicep) creates a new Subscription.
- Azure Policy automatically moves it to the Corp Management Group.
- Policy triggers the creation of a Spoke VNet and Peerings to the vWAN Hub.
- Routing Intent automatically secures the traffic without the team ever seeing a Route Table.
5. Architectural Blueprint (Summary)
| Component | Recommendation |
| Topology | Azure Virtual WAN (vWAN) Hub-and-Spoke. |
| Routing Control | Routing Intent (Standard Hub) to eliminate manual UDRs. |
| Governance | Azure Virtual Network Manager (AVNM) for global security rules. |
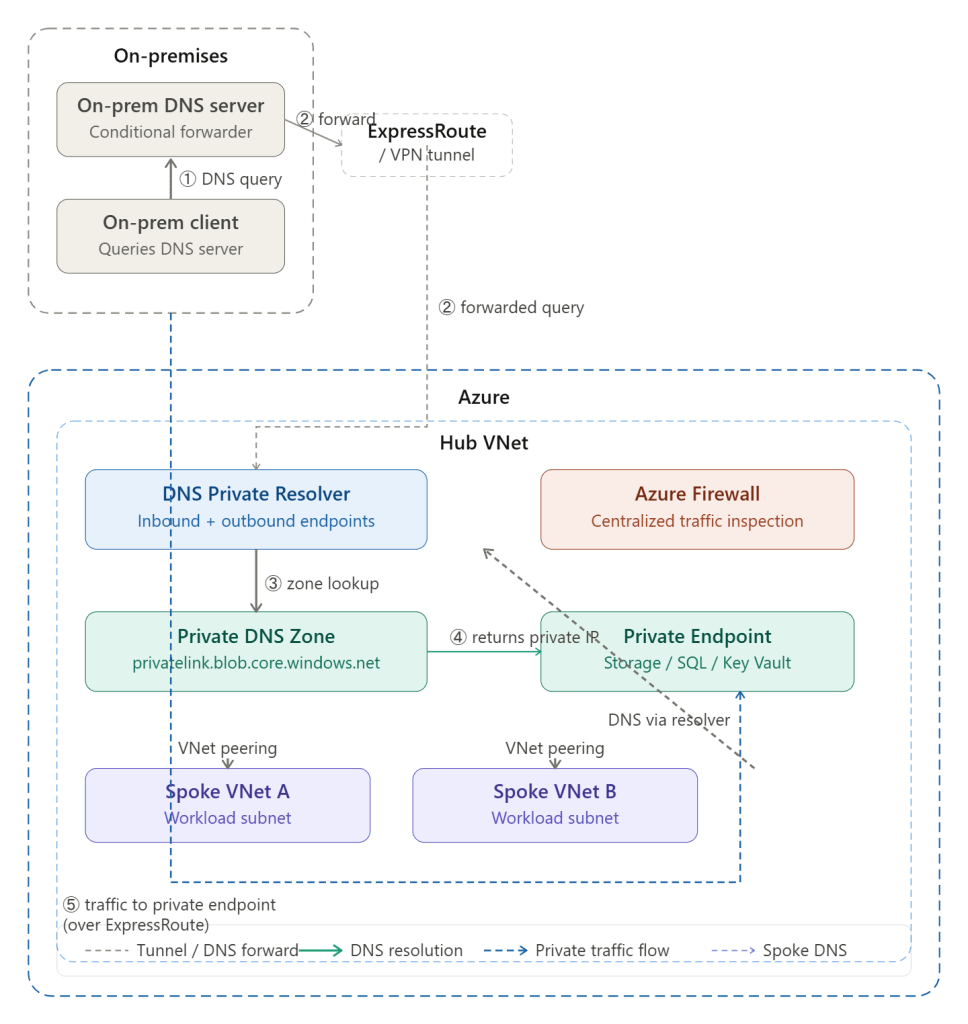
| Internal Comms | Private Link for sensitive PaaS-to-PaaS traffic (SQL, Storage). |
| Automation | Infrastructure as Code (Bicep/Terraform) via ALZ Accelerators. |
Implementation Pro-Tip
Since you are starting from scratch, ensure you implement Azure DDoS Protection on the Hub IP addresses and enable Diagnostic Settings to a central Log Analytics Workspace immediately. In 2026, observability is not an “add-on”—it’s a requirement for troubleshooting the automated routing of vWAN.
Since you’re using Terraform, you have the advantage of leveraging the Azure Verified Modules (AVM) and the ALZ (Azure Landing Zones) Terraform module. These are the industry standard for codifying the “Hub-and-Spoke” architecture with Virtual WAN.
Here is the architectural design and the strategic Terraform implementation path for your greenfield environment.
1. The Terraform-Centric Architecture
The goal is to treat your network as a “platform” that provides services to “application” spokes.
Core Components
- Virtual WAN Module: Deploys the
azurerm_virtual_wanandazurerm_virtual_hub. - Secured Hub: Deploy
azurerm_firewallwithin the hub. - Routing Intent: Configures
azurerm_virtual_hub_routing_intentto point all $0.0.0.0/0$ (Internet) and private traffic (Internal) to the firewall. - Spoke Vending: A reusable module that creates a VNet, subnets, and the
azurerm_virtual_hub_connection.
2. Recommended Terraform Structure
For a large environment, do not put everything in one state file. Use a layered approach with remote state lookups or specialized providers.
Layer 1: Foundation (Identity & Governance)
- Deploys Management Groups and Subscription aliases.
- Sets up the Terraform Backend (Azure Storage Account with State Locking).
Layer 2: Connectivity (The “Hub”)
- Deploys the vWAN, Hubs, Firewalls, and VPN/ExpressRoute Gateways.
- Crucial Logic: Define your
routing_intenthere. This ensures that the moment a spoke connects, it is governed by the central firewall.
Layer 3: Landing Zones (The “Spokes”)
- Use a Terraform For_Each loop or a Spoke Factory pattern.
- Each spoke is its own module instance, preventing a single “blast radius” if one VNet deployment fails.
3. Handling “East-West” Traffic in Code
With vWAN and Routing Intent, your Terraform code for a spoke becomes incredibly simple because you omit the azurerm_route_table.
Terraform
# Example of a Spoke Connection in Terraformresource "azurerm_virtual_hub_connection" "spoke_a" { name = "conn-spoke-prod-001" virtual_hub_id = data.terraform_remote_state.connectivity.outputs.hub_id remote_virtual_network_id = azurerm_virtual_network.spoke_a.id # Routing Intent at the Hub level handles the traffic redirection, # so no complex 'routing' block is needed here for East-West inspection.}
4. Addressing Modern Constraints (2026)
- Provider Constraints: Ensure you are using
azurermversion 4.x or higher, as many vWAN Routing Intent features were stabilized in late 2024/2025. - Orchestration: Use Terraform Cloud or GitHub Actions/Azure DevOps with “OIDC” (Workload Identity) for authentication. Avoid using static Service Principal secrets.
- Policy as Code: Use the
terraform-azurerm-caf-enterprise-scalemodule (often called the ALZ module) to deploy Azure Policies that deny the creation of VNets that aren’t peered to the Hub.
5. Summary of Design Benefits
- Zero UDR Maintenance: Routing Intent removes the need to calculate and update CIDR blocks in Route Tables every time a new spoke is added.
- Scalability: Terraform can stamp out 100 spokes in a single
plan/applycycle. - Security by Default: All cross-spoke traffic is forced through the Firewall IDPS via the Hub connection logic.
Would you like to see a more detailed code snippet for the vWAN Routing Intent configuration, or should we look at how to structure the Spoke Vending module?